Learning something new every day.
LinkedIn Learning Course – Laravel 5.6 New Features
Welcome from Laravel 5.6 New Features by Justin Yost My newest course with LinkedIn Learning and Lynda went live a few weeks ago, it covers the upgrade path to Laravel 5.6 and some of the best of the new and improved features, take a look and I hope you learn something new from it.
LinkedIn Learning Course – Consuming RESTful APIs in PHP with Guzzle
LinkedIn Learning provides online training courses in a variety of subject matters. I’ve been honored to work with them on a few different courses at this point covering primarily PHP and related topics. The latest one went up earlier this week, it covers using Guzzle to communicate with RESTful APIs. APIs are a super popular […]
Lynda Course – Test-Driven Development in PHP with PHPUnit
New Lynda course covering Test-Driven Development and PHPUnit
Meetup Talk on Generators: All About the Yield
This was a really interesting talk, especially as beforehand, I didn’t have a ton of knowledge of generators. I knew what a generator was and some of the basics, but that was about it. So I learned both about generators specifically, and some more specifically about building coroutines using a generator.
Meetup Talk on The CakePHP 3 ORM: Even More Awesome Than You Realize
Meetup talk for PHP Vegas covering some interesting aspects of the CakePHP 3 ORM.
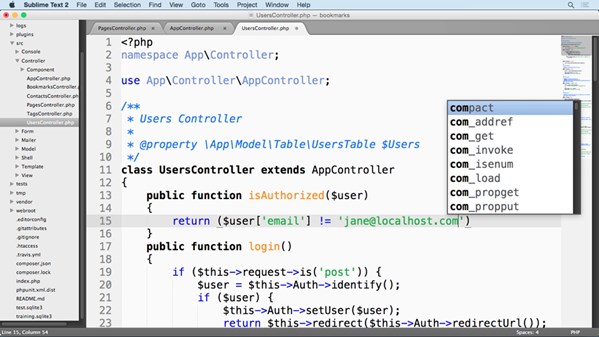
Lynda Course – Learn CakePHP 3: The Basics
Lynda.com is a website that provides online training courses in a variety of subject materials. I’ve been honored to work with them on now three separate courses. The latest one went up earlier this month, it covers some of the basics of working with CakePHP 3. Interested in working with CakePHP? You should watch the […]
Meetup Talk on Unit Testing: The Why and The How
Another talk at PHP Vegas Meetup, this one covered unit testing. I tried to split about 50% on why to do unit testing and the other 50% on some pretty basic unit tests. This was a tough talk to try hitting an hour on. I know it’s a good topic for me to talk on […]
Meetup Talk on Dependency Injection
December PHP Las Vegas Meetup talk on Dependency Injection.
Meetup Talk on PHP Namspaces and PSR-0/4
For the November PHP Meetup, I spoke on PHP Namespaces and PSR-0/4.
Meetup Talk on Building APIs
I spoke on Building APIs, focusing mostly on the upfront design of APIs, at the most recent Las Vegas PHP Meetup. Overall this was defiantly one of my better talks with lots of good feedback. One key things helped I believe in the preparation and eventual presentation of the talk. I presented a rough version […]
Got any book recommendations?